SJULTRA and runZero – an innovative CAASM solution that delivers exceptional security visibility in minutes.
SJULTRA specializes in reselling, deploying and operating runZero in complex, high-risk environments, providing active scanning, passive discovery and API integrations within a robust platform.
The goal? To provide a consolidated view of assets – both managed and unmanaged – across diverse IT, OT, IoT, cloud, mobile and remote environments.

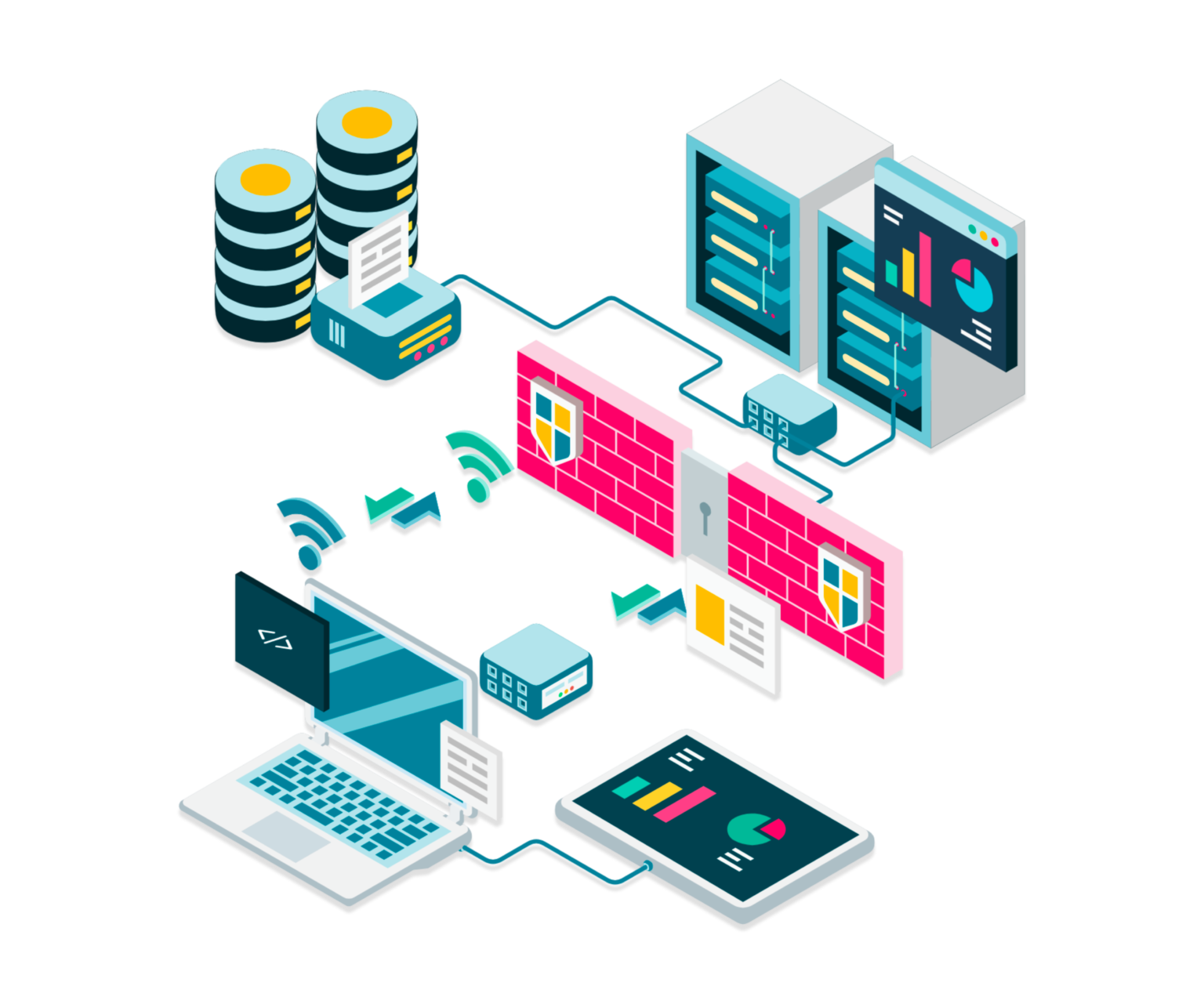
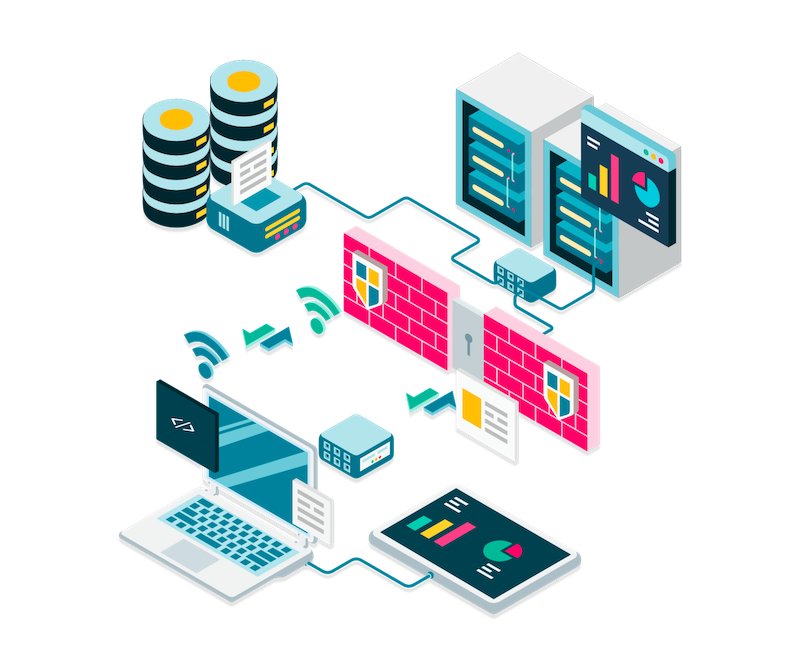
Cyber Asset Discovery
Uncover all managed and unmanaged devices, IT, IoT, and OT, from all environments, on-premises, cloud, and remote.
Cyber Asset Inventory
An inventory is only useful if there is a true understanding of assets.
Attack Surface Management
Get to full asset inventory and actionable intelligence with a CAASM solution

Cyber Hygience
Quickly respond to security incidents, and strengthen your readiness against future attacks.
Build your CAASM solution with SJULTRA and RunZero
SJULTRA are resellers and service experts, building CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More solutions with runZero.
In addition to runZero expertise, the SJULTRA team is experienced in infosec, infrastructure, and we understand that it’s not just about technology: we make sure the people and process aren’t left behind.
Ask us anything!
Do you want to discuss a challenge or solution?
. No obligation.
. Our sales won’t hound you.
. Our marketing won’t spam you.
Read more
How to reduce IT entropy caused by Joiners, Movers, and Leavers
IT entropy is cause by process break down as well as human mistakes. You need to find it before you
The Impact of Persona Groups and Use Cases on Asset and Attack Surface Management
Which persona groups and use cases are impacted by cybersecurity asset and attack surface management?
eBPF community newsletter and updates
The eCHO newsletter for the eBPF community is a goldmine of eBPF information. SJULTRA featured in Ep. 63, and we