
Home » Latest Articles » CAASM Use Case #8 – Finding Ephemeral Devices

Welcome back, digital detectives! 🕵️
We’re diving into the eighth installment of our Cybersecurity Observability use cases series. Today, we’re chasing shadows in the digital world: hunting for ephemeral devices.
Picture this: Your network is humming along… then your CISO get’s back from lunch with another CISO. She casually asks this question:
"How can we be sure our security covers devices that might only exist for a few hours or even minutes? Like the build VMs from the Dev Team's CI/CD pipeline?" (Chief Information Security Officer)
Chief Security Officer
Let’s set the stage. Ephemeral devices are the ninjas of the digital world – here one moment, gone the next. We’re talking about:
These digital ghosts pose some serious questions:
Traditional tools just can’t keep up. It’s like trying to catch smoke with a butterfly net!
This is where SJULTRA’s CAASM services, becomes your incident response nitrous boost.
It’s like giving your security team a time machine and a crystal ball, all rolled into one.
CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More pulls data from a smorgasbord of sources:
By correlating this data, CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More creates a rich, unified view of your entire digital ecosystem. It’s like having a digital map of your entire IT landscape, with every device, user, and cloud instance clearly labeled.
So, how do we catch these digital ghosts? CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More looks for telltale signs:
It’s like looking for spectral fingerprints across your network!
Let’s get practical. Here are some ghostbusting techniques… err, queries you can use…
Find devices with less than a day’s uptime.
uptime < 1 day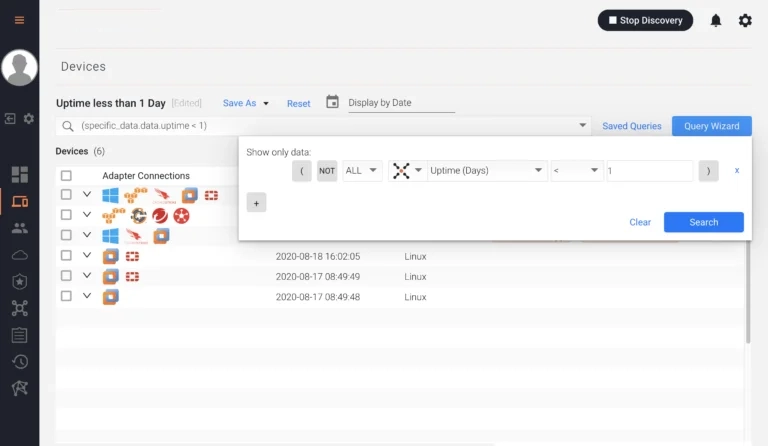
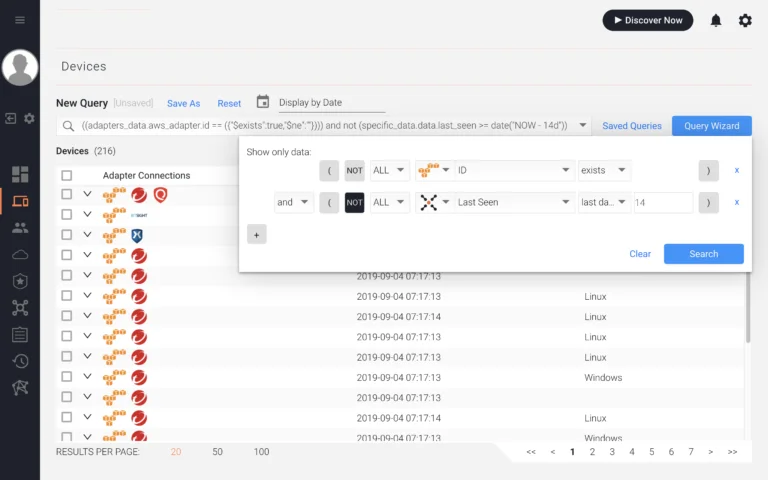
Spot cloud instances not seen in 14 days.
cloud instances not seen 14 daysGreat for finding forgotten instances that might pose risks.
Find VMs that are powered off but still in your system.
VMs Turned Off, Not Seen by CAASM in 5 Days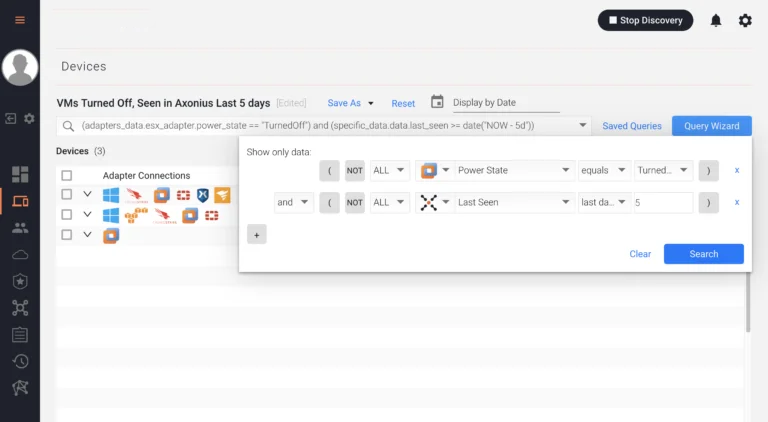
Once you’ve spotted these digital apparitions, what next? CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More lets you automate your ghostbusting:
And there you have it, digital ghostbusters! 👻
That’s how we turn the elusive challenge of ephemeral devices into a manageable, observable process. It’s not just about finding these digital ghosts; it’s about understanding and managing them in real-time.
Remember, this is just 8 out of 14 standard use cases we help our customers with as part of our CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More Concierge service. And guess what? You can get it for free!
In the world of cybersecurity, what you can’t see can definitely hurt you. But with the right tools and a bit of observability magic, we can shine a light on even the most fleeting digital shadows.
Stay vigilant, keep querying, and may all your ephemeral devices be known and managed!
Read the documentation: Finding ephemeral devices.