
Home » Latest Articles » CAASM Use Case #7 – Accelerating Cybersecurity Incident Response

Welcome back, cyber-sleuths! We’re diving (not delving! 😜) into the seventh instalment of our Cybersecurity Observability use cases series.
Today, we’re talking about something that can make or break your security team’s effectiveness: accelerating cybersecurity incident response.
How long does it take you and your team to respond to incidents? What slows you down? For most people it’s access to information because it’s spread across silos….
Picture this: It’s 2 AM, alarms are blaring, and your security analyst is desperately trying to piece together what’s happening. Then your CISO calls:
"We've got a potential breach. How long until we know what's affected and can contain it?" (Chief Information Security Officer)
Chief Security Officer
Tick tock, tick tock. Every second counts, but your analyst is drowning in a sea of disconnected data. Sound familiar? Well, buckle up, because CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More (Cyber Asset Attack Surface Management) and cybersecurity observability are about to be your incident response superchargers!
Let’s face it: incident response is a race against time. Your security analysts are often:
And with the explosion of IoT and cloud devices, it’s like trying to find a specific grain of sand on a beach. Every minute spent searching is a minute the bad guys have to wreak havoc.
If you need to ask questions that begin with "Where do I find...?" then you're already slow at cybersecurity incident response. Access to information is a leading indicator of cybersecurity incident response performance.
John Doe
Imagine if you could search across all of your cybersecurity information sources from the same place…
This is where SJULTRA’s CAASM services, becomes your incident response nitrous boost.
It’s like giving your security team a time machine and a crystal ball, all rolled into one.
CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More pulls data from a smorgasbord of sources:
By correlating this data, CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More creates a rich, unified view of your entire digital ecosystem. It’s like having a digital map of your entire IT landscape, with every device, user, and cloud instance clearly labeled.
So, how does this supercharge your incident response? Let’s break it down:
It’s like giving your analysts X-ray vision for your IT environment!
Here’s how you can use the CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More search bar to find anything you need across all of your IT/OT estate.
If an analyst receives an alert of a possible malware infection associated with the IP address: 10.0.56.104, you search for this IP address in CAASM by simply entering it into the main search bar on the dashboard:
John Doe
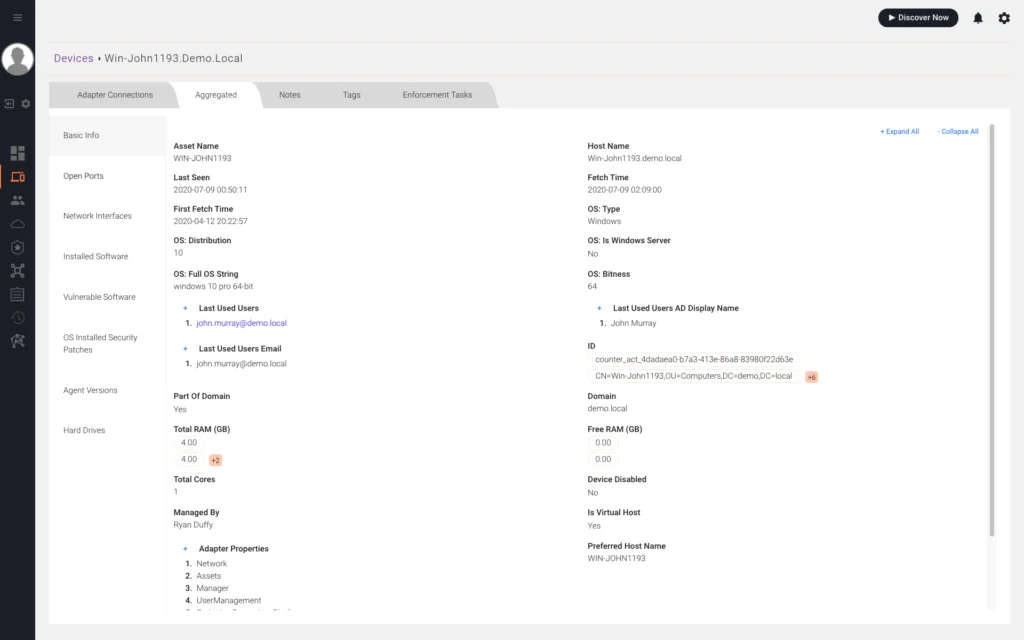
Examples of data points you can search across:
Bonus point:
Google chrome users can also search for assets directly in the address bar by adding CAASM as a search engine.
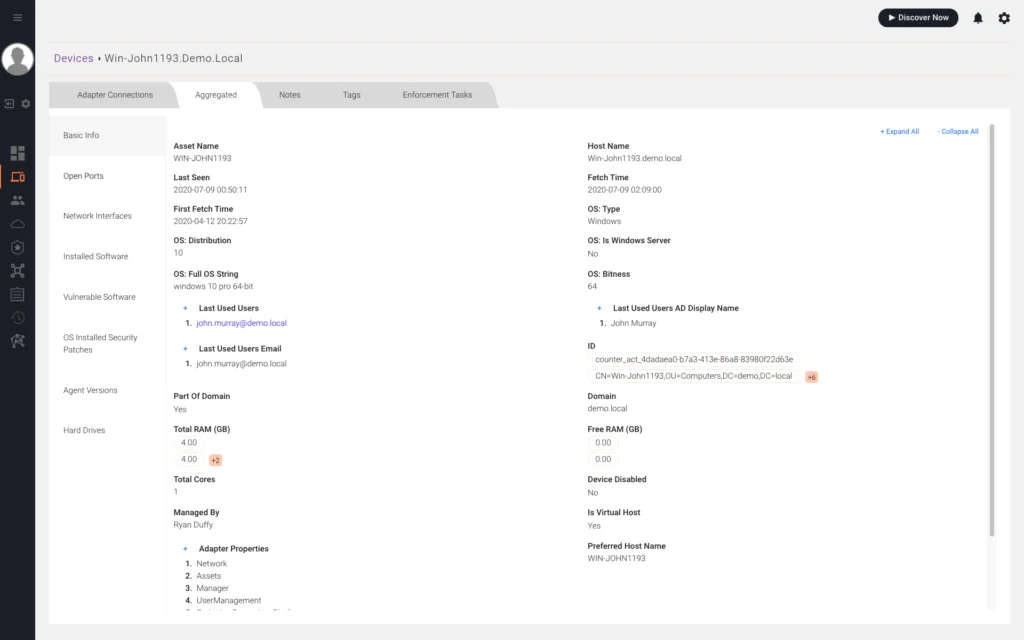
Using historical snapshots, CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More can also be used to investigate older incidents and pinpoint historical asset attributes.
By selecting the display by date on the devices or use pages, analysts can view historical asset attributes, such as:
But wait, there’s more! Once you’ve identified the affected assets, CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More lets you take immediate action:
It’s like having a cyber-SWAT team at your fingertips!
And there you have it, incident response superheroes! That’s how we turn the stress-inducing chaos of incident response into a streamlined, observable process. It’s not just about responding faster; it’s about responding smarter.
Remember, this is just 7 out of 14 standard use cases we help our customers with as part of our CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More Concierge service. And guess what? You can get it for free!
In the world of cybersecurity, time is more than money—it’s the difference between a minor hiccup and a major breach. But with the right tools and a bit of observability magic, we can turn your incident response team into digital speed demons.
Stay vigilant, keep your response times low, and may all your incidents be quickly contained!
Read the documentation: Accelerate cybersecurity incident response investigations.