
Home » Latest Articles » CAASM Use Case #5 – Finding unmanaged devices

Welcome back, cybersecurity sleuths! 🕵️
We’re diving into the fifth instalment of our Cybersecurity Observability use cases series.
Today, we’re tackling a challenge that’s like finding a needle in a digital haystack: unmanaged devices on your network.
Picture this: Your security tools are running smoothly, protecting all your corporate devices. Then your CISO drops this mind-bender:
What about the devices we don't know about? When "rogue" staff or even bad actors add devices to the network outside of our process and procedure? How can we protect what we can't see?" (Chief Information Security Officer)
Chief Security Officer
Boom! It’s the cybersecurity equivalent of dark matter – you know it’s there, but how do you find it?
Fear not! This is where CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More (Cyber Asset Attack Surface Management) and cybersecurity observability become your digital telescope.
This is what SJULTRA can help you solve with CAASM (Cyber Asset Attack Surface Management) and cybersecurity observability.
Let’s break it down. Unmanaged devices are the digital wildcards in your network. They’re IP-connected devices that are:
These could be anything from Bob from accounting’s personal smartphone to that smart TV in the conference room, or even a rogue VM someone spun up and forgot about. They’re the “unknown unknowns” that keep security pros up at night.
Who's scanning your network for unknown devices? How do you know they are "unknown"? How do you investigate them.. before banning your CEOs new mobile phone from the network? Who takes that call? 😨
John Doe
This is where SJULTRA’s CAASM services, becomes your digital detective. It’s like giving your security team over-the-horizon, long-range vision for your entire network.
CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More pulls data from multiple sources:
By correlating and deduplicating this data, we can spot the devices that are flying under your security radar.
It’s like finding Waldo, if Waldo was a potential security risk!
Once we have CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More set up (remember, SJULTRA offers a free 30-day trial), we can start hunting those elusive unmanaged devices on the network.
Show me all devices that aren't managed by any security agent or management solution.
John Doe
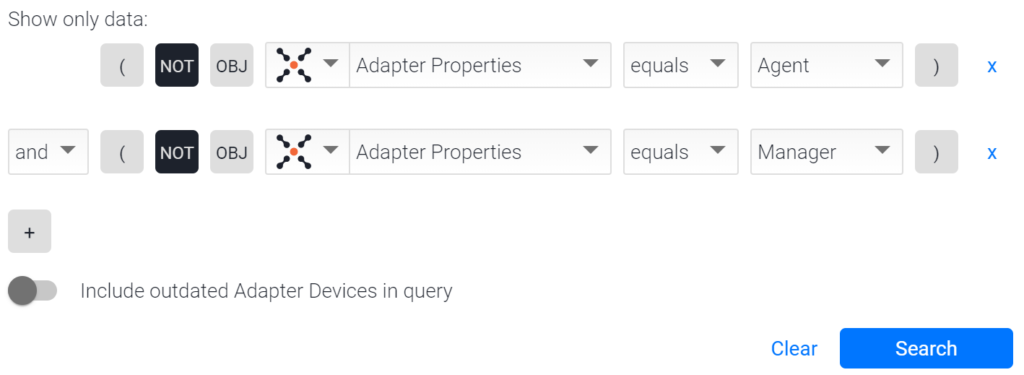
not (((specific_data.data.adapter_properties == "Agent" or specific_data.data.adapter_properties == "Manager")))
This query finds all unmanaged devices without security agents or management solutions.
Here’s an example of the returned results:

(adapters_data.aws_adapter.id == ({"$exists":true,"$ne":""})) and not specific_data.data.adapter_properties == "Vulnerability_Assessment" and (specific_data.data.software_cves.cve_id == ({"$exists":true,"$ne":""}))
But let’s be more specific.
We can add other filter criteria to prioritize which devices should be addressed. For example, let’s find unmanaged devices that are not being scanned by a VA tool.
not specific_data.data.adapter_properties == "Agent" and not specific_data.data.adapter_properties == "Manager" and not specific_data.data.adapter_properties == "Vulnerability_Assessment"
Even more specific: has this happened in the last few days?
not specific_data.data.adapter_properties == "Agent" and not specific_data.data.adapter_properties == "Manager" and not specific_data.data.adapter_properties == "Vulnerability_Assessment" and specific_data.data.last_seen >= date("NOW - 3d")
Great, we’ve uncovered these hidden cloud instances. What’s next? This is where the “action” part of our cybersecurity observability comes in. We’ve got four aces up our sleeves:
And there you have it, digital detectives! 🕵️♂️
That’s how we turn the invisible threat of unmanaged devices into a manageable, observable process.
It’s not just about finding devices; it’s about making sure we’re seeing our entire digital ecosystem, even the parts hiding in the shadows.
Remember, this is just 5 out of 14 standard use cases we help our customers with as part of our CAASM Concierge services. And guess what? You can get it for free!
In the world of cybersecurity, what you don’t know can definitely hurt you. But with the right tools and a bit of observability magic, we can shine a light on those hidden corners of your network.
Stay vigilant, keep querying, and may all your devices be known and managed!
And don’t forget our no catch, no cost, no obligation, limited time free CAASM trial offer.
Read the Documentation: Finding Unmanaged Devices.