
Home » Latest Articles » CAASM Use Case #11 – Managing Windows and Linux Servers

In the world of cybersecurity, an unmanaged server is like an unlocked door in your digital fortress. And it only takes one unlocked door to give them the keys to the castle.
John Doe
Welcome to the eleventh installment in our series exploring the practical applications of Cyber Asset Attack Surface Management (CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More).
Today, we’re diving into a critical use case: managing Windows and Linux servers across your organization.
Imagine this scenario: You’re a system administrator tasked with ensuring all servers in your environment are up-to-date, properly configured, and secure.
But with servers scattered across on-premises data centers and multiple cloud platforms, how can you maintain a comprehensive view of your server landscape?
Your server inventory must be three things:
This blog post introduces how to start improving your server inventory with CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More.
Why is a credible, accurate, comprehensive server inventory important? Because if it's not, then you're going to miss problems, and when incidents happen you won't have the information to make timely and correct decisions -- further compounding your bad situation.
John Doe
Servers are the backbone of any organization’s IT infrastructure.
Whether on-premises or in the cloud, Windows and Linux servers host critical business applications and often process sensitive data.
Maintaining an accurate inventory of these servers, including their operating systems, versions, resources, configurations, installed software, and associated users, is crucial for protecting your organization’s infrastructure.
Managing servers and their operating systems comes with several challenges.
Not addressing these challenges is leaving the proverbial door open to bad actors.
This is where SJULTRA’s CAASM services, becomes your incident response nitrous boost.
It’s like giving your security team a time machine and a crystal ball, all rolled into one.
CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More pulls data from a smorgasbord of sources:
By correlating this data, CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More creates a rich, unified view of your entire digital ecosystem. It’s like having a digital map of your entire IT landscape, with every device, user, and cloud instance clearly labeled.
Start by connecting to key data sources such as:
There are a couple of steps to this.
First, create a chart of known operating systems from your data sources — let’s see what you’ve got!
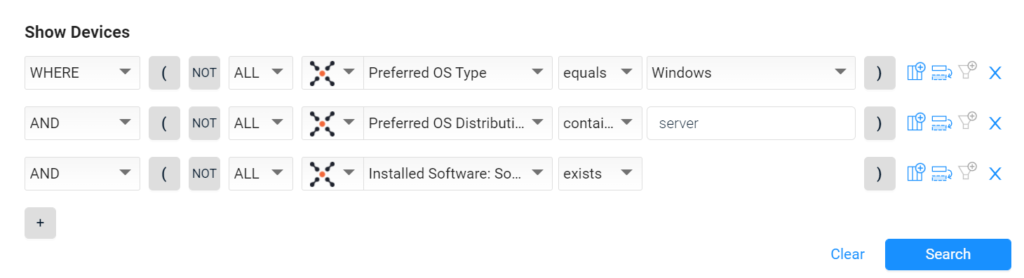
Second, use the CAASM Query Wizard to create targeted queries such as “Find all Linux servers and their distributions”
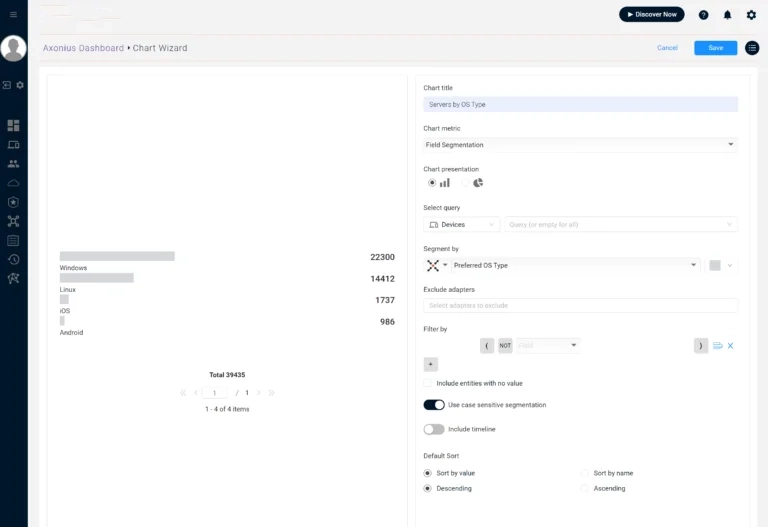
To start focusing on Linux and Windows, you can create a new query and a new chart for that.
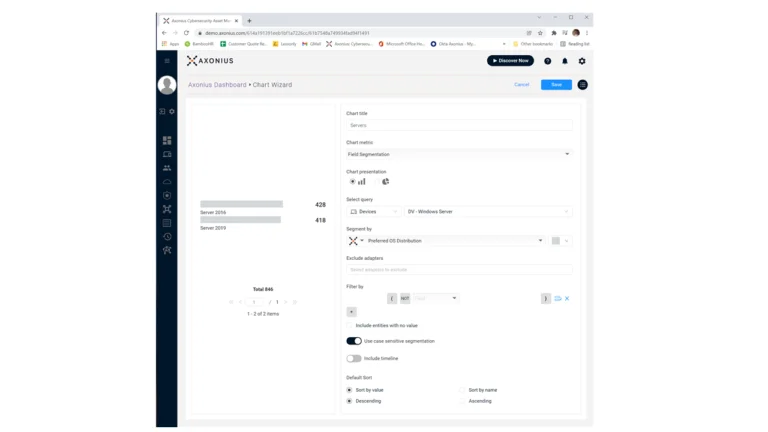
For example, this query and chart combination will first find all your Windows serers:
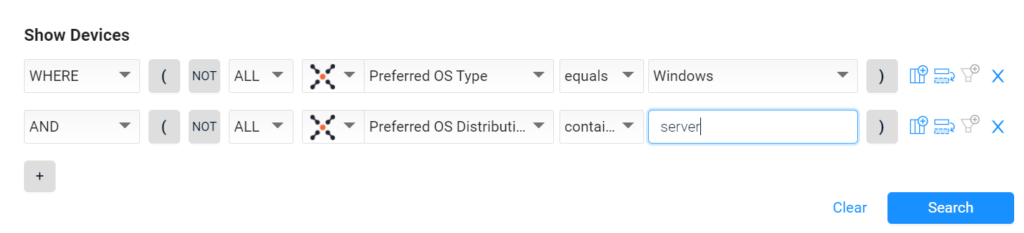
Then you can create a chart based on that query:
Create queries to track server resources.
Add columns for Total RAM, Free RAM, Hard Drives: Size, and Hard Drives: Free Size to your query results.

Now, based on your query… and then your chart… you can quickly see server resources across your whole estate in one place.

Find servers with critical vulnerabilities:
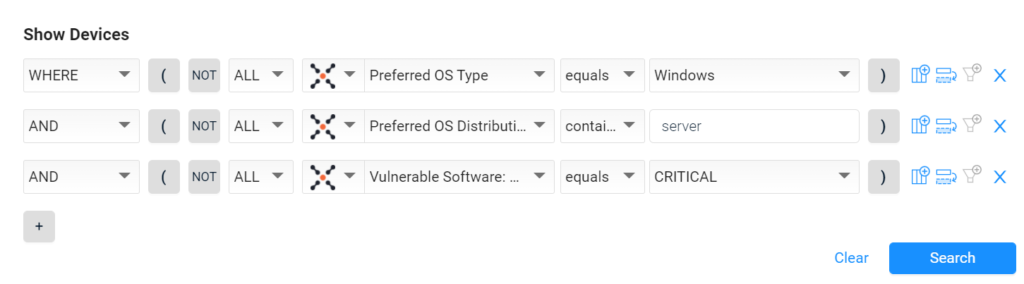
Identify servers without vulnerability assessment tools:

This level of detail is particularly useful when you need to quickly find if you are exposed to X threat on Y software.
For example, threats can apply to only specific product versions so being able to quickly find if you have that version is key to accelerating incident response.
Once you’ve identified issues or discrepancies in your server inventory, SJULTRA CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More allows you to take immediate action:
Maintaing a Windows and Linux server inventory — that is accurate, credible, comprehensive — is crucial for maintaining a robust and secure IT infrastructure.
With SJULTRA CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More, you can transform this challenging task into a streamlined, automated process.
Remember, this is just one of the 14 powerful use cases for CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More. Stay tuned for our next instalment to discover more ways to enhance your cybersecurity posture.
Ready to sort out your user inventory? Start your free trial of SJULTRA CAASM today!
Read the CAASMCyber Asset Attack Surface Management (CAASM) focuses on man… More documentation: Manage Windows and Linux Servers.